Get a good pop-up blocker. My ISP has a Anti-Virus for free. Yours could as well. A lot of popular ISPs have free Anti-Virus software available.
Google Chrome and then use an extension on personal computers.
On Android, follow the below...
Turn pop-ups on or off
- On your Android phone or tablet, open the Chrome app
.
- To the right of the address bar, tap More
Settings.
- Tap Site settings
Pop-ups.
- Turn Pop-ups to Allowed or Block.
Stratics shouldn't be held accountable for poor internet etiquette. It's 2018 and malicious people are constantly thinking of new ways of exploiting people. You can either be the exploited your you can do your best to not be. Don't get me wrong... If a expert wants to be malicious to you, they can. There's very little you can do if a person targets you if that person has a good tool set.
The most common attacks you should always keep yourself from are below...
Phishing, this is where someone fakes a website so you think you're using a legitimate site, but you aren't. Common forms of this are emails with links. Always check the url. Google the company separately and see what url they are at. A web url is broken into three parts. HTTP (or HTTPS) is the protocol.
www.google.com is the domain. / and after are specific files or folders. Basic SQL can also be included in a weburl, but you should make sure the domain matches the website you find on Google. It becomes easier and easier as you start remembering your favorite sites domains. Other common ways to identify a phishing attempt is stressing time or stressing a punishment. If they say you only have such and such time to do it or if they say that if you don't there will be some negative affect... these are common to phishing.
Treat hyperlinks on any communication medium the same as an email. If someone links something in a forum, for example... google it and make sure you're going where you think you're going.
Social Engineering , is where someone personally tries to get you to give little pieces of information you don't realize the impact of. The most common way this happens is phone call. If someone calls you asking for information ask them for a website to go to for resolution instead. Google what they're telling you to see if someone else has had the same call. If someone tells you that you owe them money and you don't know about it, don't pay them. Ask them to mail you a letter with the bill. People who can socially persuade people are very very good at it. You'd be surprised what you can get people to do. Protect your information from people you trust as well because they can be targeted for your information.
Virus, A virus attaches itself to a .exe or replaces it altogether. A trojan horse is something that is disguised as a harmless application. You think you're downloading a registry scanner for example, and it's really set to scan your files and send them to someone else. The best way to prevent this is to keep your anti-virus updated and set to scan often. This is reactive. Firewalls can also stay updated to prevent it altogether. A firewall is like a filter that filters out virus. A Anti-Virus finds it if it goes through the firewall. Both are fallible because it requires the attack to be known before it can filter or remove it. For the average user this isn't a problem, but if you're targeted (DOUBTFUL) it's easy to get around.
Worm, A worm is it's own program where a virus attaches itself to a program. That's the difference. A worm will overwhelm memory and create exploits for other attacks or destroy your computer memory. (There are many kinds of memory.) The worst memory to get hit is your ROM. Your ROM is a static memory on your motherboard that runs basic BIOS. This will permanently kill your computer. Attacks on your RAM or Hard Drive memory are easy to mitigate. RAM is non-consequential for the most part depending on the attack. Hard Drive is mitigated by creating a back-up. You should always have back-ups.
Two newest attacks (Spectre and Meltdown), and you are affected because everyone pretty much is, is that your processors work faster than your transmissions of information between applications. People are able to process scripts so fast because of your processor that it picks up your packets of information before they are transmitted and encoded. They've patched them, but it's another ongoing attack that's new so I have very little information on it. Where applications usually are isolated, now because processors are so fast, information on one application is accessible to be read when it normally won't be. (Chrome passwords saved, for example.) The mitigation here is to stay patched up with your OS, but it's an ongoing risk.
Steps you can take on your own and stop relying on Stratics to protect you are....
Identify your assets. What do you have that is useful to someone else?
Identify vulnerabilities in your assets. Where don't you have a mitigation?
Identify threats that attack those vulnerabilities from the above.
Create your mitigation plans for the threats.



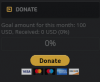
 , just making sure everyone is informed on other solutions. Oh and here's another one which also gives you Ad-Free Browsing for a month
, just making sure everyone is informed on other solutions. Oh and here's another one which also gives you Ad-Free Browsing for a month